[ad_1]
Single sign-on options are safety software program merchandise that sometimes fall below the id and entry administration (IAM) umbrella. SSO merchandise assist groups handle consumer identities, each staff and prospects, and grant and restrict their entry to firm functions. They play a essential position in defending delicate knowledge and functions as a result of SSO reduces password sprawl and limits the time window through which a risk actor might hack an utility.
Listed here are our high six alternatives for the perfect SSO options:
- Okta: Greatest general SSO resolution for a mixture of pricing and options
- OneLogin: Greatest resolution for sandboxing and DevSecOps groups
- Microsoft Entra ID: Greatest SSO choice for Home windows environments
- JumpCloud: Greatest product for Linux customers and multi-platform groups
- Ping Id: Greatest for a mixture of id orchestration and entry insurance policies
- CyberArk: Greatest SSO resolution for native consumer conduct analytics
Prime Single Signal-On Options In contrast
Beneath, we’ve given an summary of our high six picks and some of their options, like privileged entry administration and templates for id workflows, in addition to pricing.

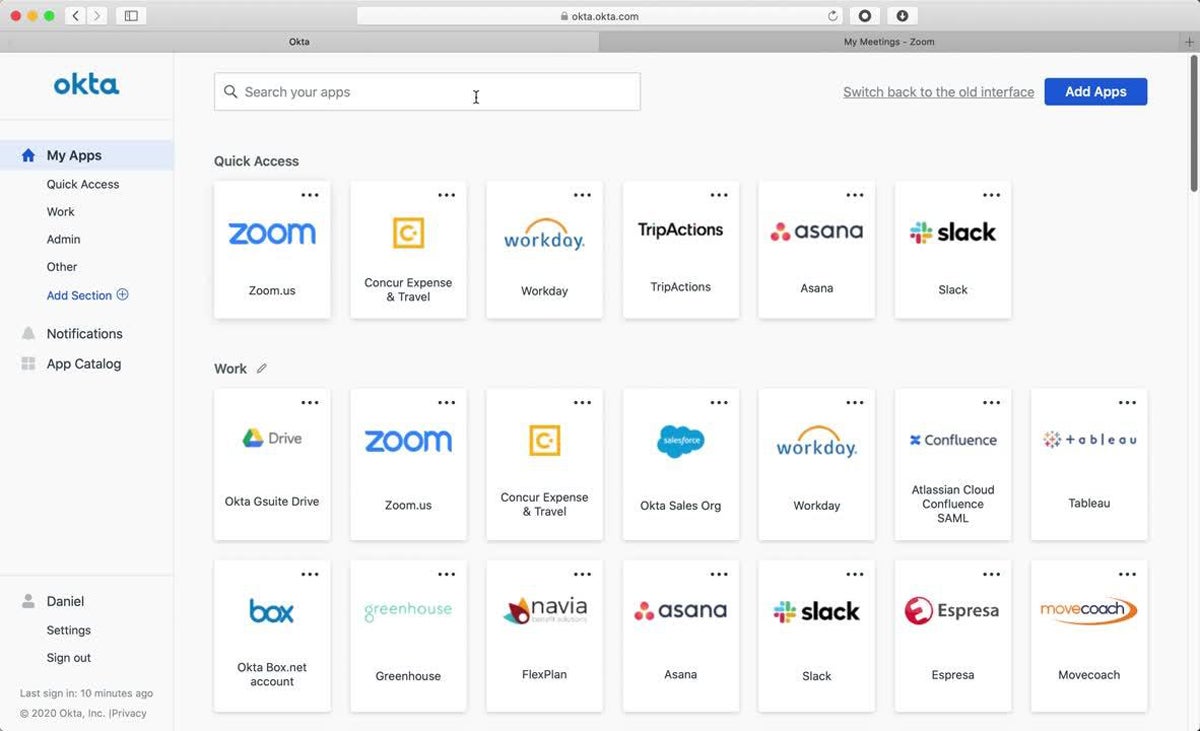
Okta
Greatest Total SSO Answer for Pricing & Options
Total Ranking: 4.6/5
- Core options: 4.8/5
- Integrations: 5/5
- Superior options: 5/5
- Usability and administration: 3.3/5
- Pricing: 5/5
- Buyer help: 4.4/5
Okta is a well-established IAM and SSO supplier providing a slew of id administration options, together with short-term entry and gadget assurance insurance policies. Take into account Okta if your enterprise makes use of a number of functions; as a result of Okta presents hundreds of prebuilt app connectors, it’s among the best SSO options for shielding massive software program ecosystems. Okta additionally has a clear pricing construction, permitting groups to select and select the options they want.
Okta is a incredible IAM and single sign-on product for a lot of companies, however it might be too costly for very small companies. Take into account OneLogin when you’re searching for a cheaper bundled characteristic set.
Professionals & Cons
| Professionals | Cons |
|---|---|
| Big collection of IAM options | Lacks e-mail help |
| Developer platform accessible | Doesn’t help Linux gadgets |
| Connects with over 7,000 functions | Costs for a number of options can rapidly add up |
Pricing
- SSO: $2 per consumer monthly
- MFA: $3 per consumer monthly
- Lifecycle Administration: $4 per consumer monthly
- Workflows: $4+ per consumer monthly as much as 50 flows
- Annual contract minimal: $1,500
- Free trial: 30 days
Key Options
- Id governance: Admins can approve customers’ utility entry requests and think about compliance-minded studies.
- Privileged entry: Develop customized approval processes and combine with Okta’s Entry Request options.
- Gadget assurance insurance policies: Create and handle insurance policies to permit or deny particular gadgets primarily based on standards like utilized patches.
- No-code customized branding: Customise your login pages so that they suit your group’s general model.

OneLogin
Greatest Answer for Sandboxing & DevSecOps Groups
Total Ranking: 4.5/5
- Core options: 5/5
- Integrations: 4.8/5
- Superior options: 2.9/5
- Usability and administration: 4.5/5
- Pricing: 5/5
- Buyer help: 4.4/5
OneLogin is an enterprise-grade IAM platform for each workforces and prospects, providing MFA, superior listing options, and cell id administration. OneLogin is especially suited to developer groups, with a command line device, an API, and sandboxing that enable groups to check id processes whereas they’re nonetheless in improvement. Take into account OneLogin on your DevSecOps groups in the event that they need to carefully configure your organization’s IAM processes.
OneLogin doesn’t have some options like short-term entry and drag-and-drop workflows, so in case your workforce wants these options, think about Okta as a substitute. Like OneLogin, it additionally presents a developer program and sandboxing.
Professionals & Cons
| Professionals | Cons |
|---|---|
| Developer platform accessible | Lacks short-term entry options |
| Big selection of core options | Lacks drag-and-drop workflows |
| Out there as a managed service | Doesn’t help Linux gadgets |
Pricing
- Superior plan: $4+ per consumer monthly when bundled
- Skilled plan: $8+ per consumer monthly when bundled
- SMB pricing: Specialised pricing choices accessible for companies below 50 staff
- Free trial: 30 days
Key Options
- Sandboxing: Groups can take a look at their IAM configurations earlier than pushing ultimate modifications to finish customers.
- OneLogin Entry: Sync entry to your cloud and on-premises apps utilizing OneLogin’s unified entry administration product.
- Onboarding and offboarding: Handle your consumer id lifecycles, together with deactivating their entry to firm apps.
- Good Hooks: This product permits groups to customise their very own id workflows with serverless code.

Microsoft Entra ID
Greatest SSO Choice for Home windows Environments
Total Ranking: 4.3/5
- Core options: 4.8/5
- Integrations: 4.7/5
- Superior options: 4.3/5
- Usability and administration: 4.4/5
- Pricing: 5/5
- Buyer help: 1.6/5
Microsoft Entra ID is an id governance and administration platform that’s significantly suited to current Home windows organizations. It natively integrates with different Microsoft merchandise like Sentinel and Defender for Cloud, sharing info between the merchandise so prospects can sync their safety knowledge and scale back extreme cloud permissions. Key options to spotlight embrace passwordless authentication, lifecycle administration, and customized session size.
Microsoft isn’t as clear about its buyer help availability as a number of the different distributors on this listing. For those who’re searching for a number of help channels, think about CyberArk — it additionally has drag-and-drop id workflow choices, like Entra ID.
Professionals & Cons
| Professionals | Cons |
|---|---|
| Loads of core and superior IAM options | Doesn’t help Linux gadgets |
| Out there as a cloud-based service | Restricted drag-and-drop workflow performance |
| Help for each cloud and on-premises apps | Help workforce availability is unclear |
Pricing
- Free plan: Affords some partial IAM options
- Entra ID P1: $6 per consumer monthly
- Entra ID P2: $9 per consumer monthly
- Free trial: 30 days
Key Options
- Passwordless authentication: Use texts, keys, or biometrics to log into your enterprise functions.
- Conditional entry: Components like location and session danger assist Entra ID determine whether or not to permit utility entry.
- Privileged id administration: Restrict utility utilization with just-in-time entry and simply sufficient entry.
- Person administration: All staff have an interface that permits them to handle their very own accounts, functions, and teams.
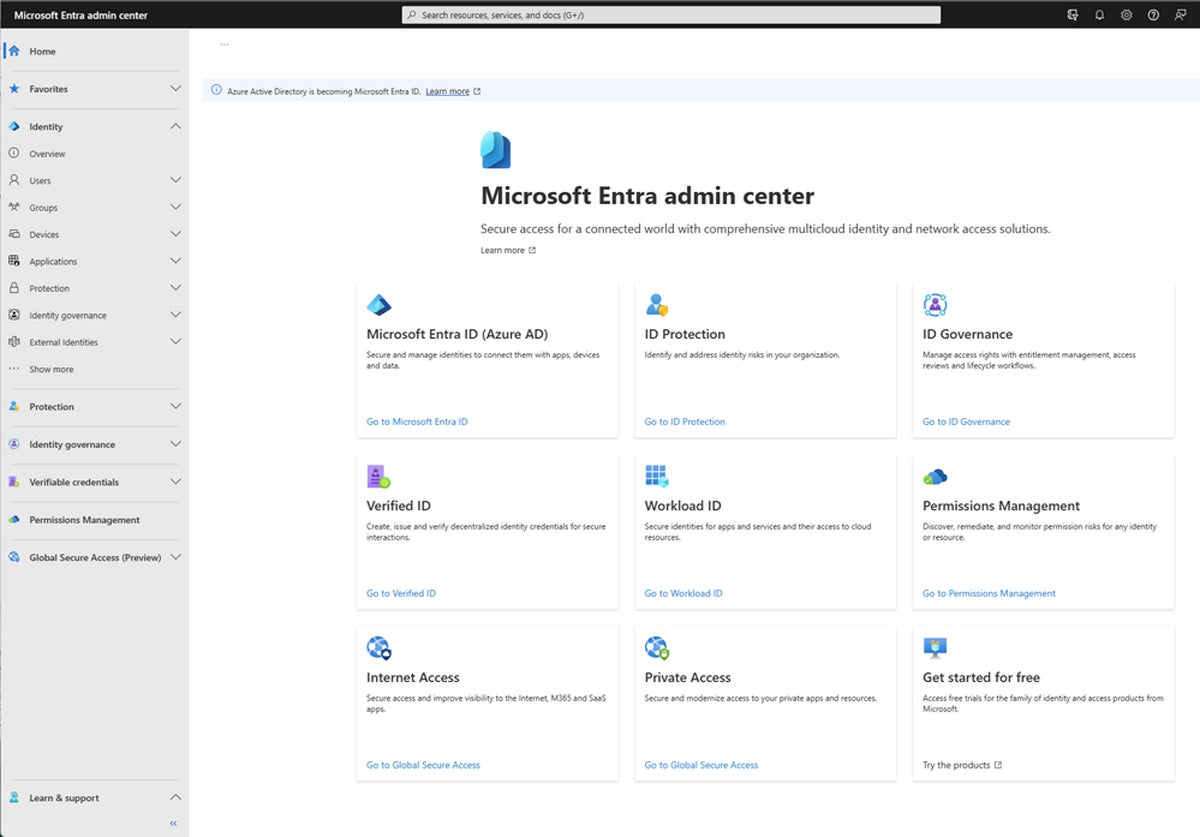

JumpCloud
Greatest Product for Linux Customers & Multi-Platform Groups
Total Ranking: 4.2/5
- Core options: 4.3/5
- Integrations: 4.3/5
- Superior options: 3.5/5
- Usability and administration: 3.3/5
- Pricing: 5/5
- Buyer help: 4.9/5
JumpCloud is an SSO vendor with loads of core id and entry administration options and a number of buyer help channels, together with cellphone and e-mail. As the one vendor on our listing that helps Linux gadgets, it’s superb for companies that use all three main working techniques — JumpCloud could be put in on macOS and Home windows too. JumpCloud additionally helps a number of cell gadgets; think about it for groups that rely closely on cell and are often on the go.
JumpCloud doesn’t supply drag-and-drop workflows, so if that’s vital to your safety workforce, think about CyberArk — it additionally presents cell gadget administration options. However understand that not one of the different choices on our listing help Linux gadgets.
Professionals & Cons
| Professionals | Cons |
|---|---|
| Helps all three main working techniques | Lacks drag-and-drop workflow performance |
| Cellular gadget administration accessible for BYOD | Unclear whether or not it’s accessible as a service |
| A number of help channels accessible | Integration catalog could be laborious to go looking |
Pricing
- SSO: $11 per consumer monthly, billed yearly
- Core Listing: $13 per consumer monthly, billed yearly
- Platform: $19 per consumer monthly, billed yearly
- Platform Prime: $24 per consumer monthly, billed yearly
- Free trial: 30 days
Key Options
- Patch administration: Groups can automate patching procedures for Home windows, macOS, Ubuntu Linux, and net browsers.
- HRIS integrations: JumpCloud presents a number of HR software program connectors, together with Paylocity and BambooHR.
- Lifecycle administration: Carry out worker onboarding and onboarding and handle all distant customers.
- Customized session size: Change your group’s consumer session size primarily based in your safety necessities.

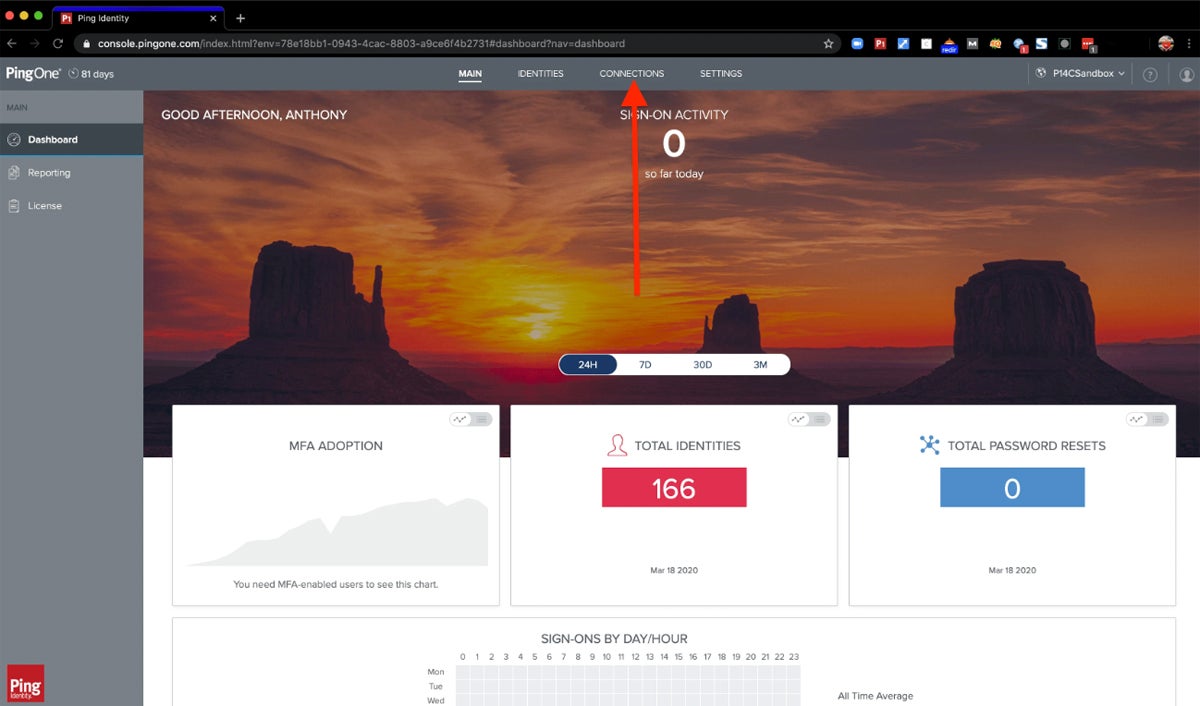
Ping Id
Greatest for a Mixture of Id Orchestration & Entry Insurance policies
Total Ranking: 4.1/5
- Core options: 4.8/5
- Integrations: 4.3/5
- Superior options: 3.3/5
- Usability and administration: 3.7/5
- Pricing: 3.8/5
- Buyer help: 4.4/5
Ping Id is an id orchestration, SSO, and entry administration product for companies of all sizes. Its key options embrace drag-and-drop id administration workflows, passwordless authentication, and customizable branding. Take into account Ping if you wish to deeply customise your enterprise’s id processes — its drag-and-drop configurations give each skilled and junior staff loads of room to tailor workflows primarily based on firm wants.
Ping is a superb selection for easy-to-use id workflows, however it lacks privileged entry administration options. Take into account CyberArk if your enterprise wants each id orchestration and privilege entry administration capabilities.
Professionals & Cons
| Professionals | Cons |
|---|---|
| Robust id orchestration capabilities | Lacks privilege entry administration |
| Helps each cloud and on-premises apps | No short-term SSO entry |
| 24/7 help for extreme instances and outages | Doesn’t help Linux gadgets |
Pricing
- Important: $20,000+ per yr
- Plus: $40,000+ per yr
- Premium: Customized pricing
- Free trial: 30 days
Key Options
- Id orchestration: Use drag-and-drop to create id workflows custom-made to your enterprise’s wants.
- Passwordless sign-on: Companies can use different authentication strategies, like biometrics, to scale back password dangers.
- Customized branding: Use Ping’s branding choices to customise your workforce’s registration and verification pages.
- Conditional entry: By way of an integration with Azure Lively Listing, grant conditional entry to customers.

CyberArk
Greatest SSO Answer for Native Person Behavioral Analytics
Total Ranking: 3.8/5
- Core options: 4.2/5
- Integrations: 4.3/5
- Superior options: 4.8/5
- Usability and administration: 2.6/5
- Pricing: 2/5
- Buyer help: 4.9/5
CyberArk is an id and SSO supplier that gives no-code, drag-and-drop id workflows for groups of any expertise degree. It’s a powerful selection for companies searching for a transparent id visualization product. One other space the place CyberArk actually shines is in its behavioral analytics product: It presents detailed studies for compliance and AI-based log assessments, and it’s a helpful useful resource for safety groups that need to carry out superior analytics.
Whereas CyberArk has incredible id orchestration options, it lacks clear pricing, so when you’re searching for a platform with analytics and extra clear pricing, think about Okta. It presents orchestration, safety analytics, and detailed pricing info.
Professionals & Cons
| Professionals | Cons |
|---|---|
| Detailed behavioral analytics | Lacks clear pricing |
| In depth id orchestration capabilities | Restricted conditional entry performance |
| A number of buyer help channels | CyberArk’s encryption procedures are unclear |
Pricing
- Contact for quote: Customized pricing accessible
- Free trial: 30 days
Key Options
- Privilege entry administration: Handle insurance policies that implement safety for all of your privilege entry accounts.
- Customized consumer classes: Admins can regulate the size of an SSO session for elevated or decreased safety.
- Customized branding: CyberArk has a number of customization choices, together with background photographs and colours.
- Person provisioning: Automated lifecycle administration options embrace provisioning accounts and flagging unmanaged accounts.

Prime 5 Options of Single Signal-On Options
SSO options typically fall below id and entry administration platforms, like most of the choices on this information, and have many comparable characteristic units. When searching for SSO or IAM instruments, search for capabilities like prebuilt integrations, consumer provisioning, branding and workflow customization, and utilization studies.
Integrations
One of many high advantages of SSO merchandise is their integration with quite a lot of enterprise software program, together with CRM and gross sales platforms, challenge administration instruments, HR apps, and different cybersecurity merchandise. The extra apps an SSO resolution helps, the higher, and groups ought to search for SSO instruments that help the bulk or all of their enterprise apps, whether or not via pre-built integrations or APIs. Broad app protection helps defend the broader enterprise community.
Person Provisioning
Person provisioning processes assist groups extra simply onboard new staff or third events into an SSO product. In some bigger IAM merchandise, like many on this listing, consumer provisioning falls below id lifecycle administration. Lifecycle administration oversees all the consumer id course of, from preliminary account activation to deprovisioning when the worker leaves the corporate.
Customized Branding
Ideally, single sign-on options ought to have customized branding choices so companies can add their very own logos and types to the principle SSO web page. That is significantly useful for managed service suppliers or organizations providing SSO to their prospects — their login pages will probably be particular to their enterprise and look extra skilled.
Straightforward-to-Use Id Workflows
SSO merchandise also needs to have customizable workflows so safety and IT groups can design id lifecycles that work greatest for his or her enterprise. Workflows are merely the recipes that designate how an IAM course of works — for instance, solely permitting an admin to log into an IT administration utility throughout sure hours. One widespread usability characteristic is drag-and-drop performance, so groups with out coding expertise can nonetheless design workflows.
Reporting
SSO merchandise ought to supply utilization studies so IT and safety leaders can monitor general id and entry tendencies, in addition to any regarding anomalies. Stories can embrace components like variety of logins in a given time frame, common session size, or present credential standing. Reporting can be vital for presenting clear, easy info to enterprise leaders who don’t know as a lot about cybersecurity patterns.
How We Evaluated the Greatest Single Signal-On Options
To pick out the perfect SSO options, we created a product rubric that analyzed software program utilizing six main classes. Every class had a particular weight and included subcriteria with their very own weighting. Every SSO product’s complete rating was decided by what number of subcriteria it met. The six merchandise that scored highest on our rubric made the ultimate listing. The ultimate scores and our broader product analysis helped us decide the use instances for our high choices.
Analysis Standards
In our foremost six classes, we first evaluated core options, comparable to MFA, workflows, and cell performance. Then we checked out integrations, together with prebuilt CRM, service desk, and cybersecurity connectors, and superior options like short-term entry. Usability and administration included standards like documentation and vendor encryption. Lastly, we checked out availability of pricing plans and buyer help channels.
- Core options (25%): We evaluated key options like MFA, workflow templates, and consumer provisioning.
- Integrations (20%): We rated merchandise primarily based on variety of integrations, particular connector choices, and Lively Listing integrations.
- Superior options (15%): Our alternatives for superior options included passwordless authentication and short-term SSO entry.
- Usability and administration (15%): We scored merchandise primarily based on performance like help for cell gadgets and completely different working techniques.
- Pricing (15%): We checked out pricing plan availability and transparency, billing choices, and free product trials.
- Criterion winner: A number of winners
- Buyer help (10%): We thought of components like cellphone and e-mail help and demo availability.
- Criterion winner: A number of winners
Ceaselessly Requested Questions (FAQs)
How Does SSO Work?
Single sign-on options use authentication tokens to confirm a sound consumer session. If a consumer registers with an SSO or IAM resolution, any utility linked to the SSO product will acknowledge the consumer’s token. If the consumer has already logged in and their session remains to be energetic, the requested utility will clear their authentication token and so they can enter. In the event that they haven’t logged in or their session is not energetic, the browser will immediate them to log in once more.
Why Is SSO Wanted?
SSO reduces the variety of account passwords that enterprise house owners want to recollect and permits them to simply log into a number of functions for under a set period of time. Brief session lengths scale back the chance for an attacker to hack a consumer account and do important harm.
Different options adjoining to SSO, like id lifecycle administration and privilege entry administration, assist companies carefully handle their customers’ accounts and permissions. This reduces alternatives for risk actors, whether or not inside or exterior, to make the most of delicate functions they shouldn’t be accessing. It additionally will increase enterprise visibility of the methods and instances customers are accessing apps to allow them to extra simply detect anomalies.
Is SSO a Safety Threat?
Total, SSO is designed to enhance enterprise safety by streamlining utility passwords and requiring data that solely the consumer ought to have or know. However in uncommon instances, if a risk actor breaches an SSO account, they’ll have entry to all of the consumer’s linked functions, not only one or two. SSO does pose dangers, as any software program options do, however its advantages outweigh potential safety drawbacks. Simply be sure to pair SSO with different safety measures.
Backside Line: SSO Is One A part of a Robust IAM Technique
Single sign-on and different merchandise inside the broader IAM class assist companies handle massive numbers of customers and their capability to entry functions and knowledge. The extra staff and functions you have got, the extra essential SSO is. Whereas it’s a useful gizmo for lowering password sprawl and safety points, it’s most helpful when used with a spread of IAM options, like privileged entry and id lifecycle administration.
Subsequent, take a look at our purchaser’s information for id and entry administration instruments to study extra about IAM.
Drew Robb contributed to this text.
[ad_2]


