[ad_1]
Roughly 9 years in the past, KrebsOnSecurity profiled a Pakistan-based cybercrime group known as “The Manipulaters,” a sprawling website hosting community of phishing and spam supply platforms. In January 2024, The Manipulaters pleaded with this creator to unpublish earlier tales about their work, claiming the group had turned over a brand new leaf and gone official. However new analysis means that whereas they’ve improved the standard of their services, these nitwits nonetheless fail spectacularly at hiding their unlawful actions.
In Could 2015, KrebsOnSecurity printed a quick writeup in regards to the brazen Manipulaters workforce, noting that they freely operated tons of of internet sites promoting instruments designed to trick individuals into giving up usernames and passwords, or deploying malicious software program on their PCs.
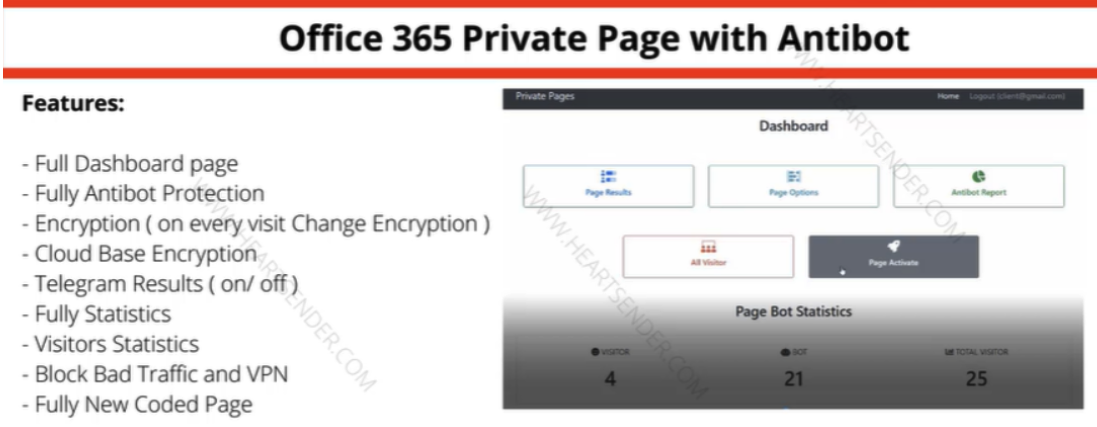
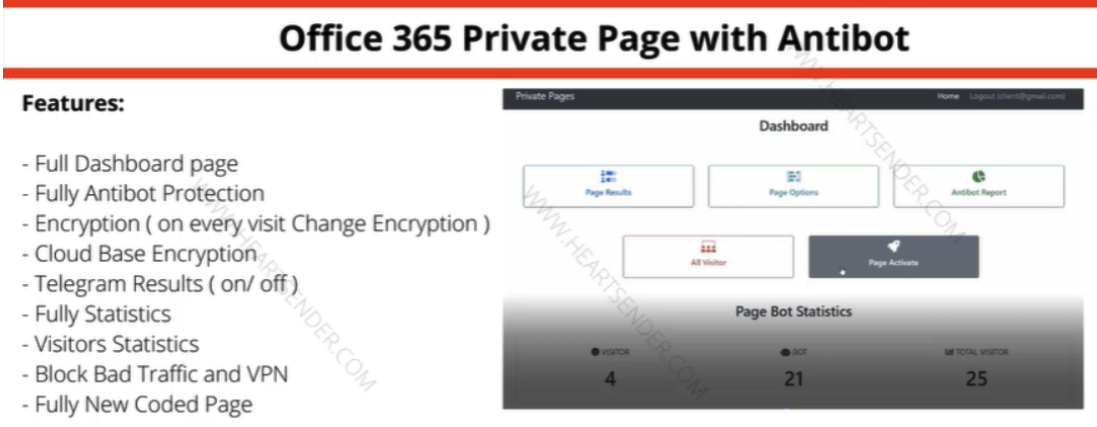
Manipulaters commercial for “Workplace 365 Non-public Web page with Antibot” phishing package bought on the area heartsender,com. “Antibot” refers to performance that makes an attempt to evade automated detection methods, preserving a phish deployed so long as attainable. Picture: DomainTools.
The core model of The Manipulaters has lengthy been a shared cybercriminal identification named “Saim Raza,” who for the previous decade has peddled a well-liked spamming and phishing service variously known as “Fudtools,” “Fudpage,” “Fudsender,” “FudCo,” and many others. The time period “FUD” in these names stands for “Fully Un-Detectable,” and it refers to cybercrime assets that may evade detection by safety instruments like antivirus software program or anti-spam home equipment.
A September 2021 story right here checked in on The Manipulaters, and located that Saim Raza and firm have been prospering below their FudCo manufacturers, which they secretly managed from a entrance firm known as We Code Options.
That piece labored backwards from all the identified Saim Raza e mail addresses to establish Fb profiles for a number of We Code Options workers, lots of whom may very well be seen celebrating firm anniversaries gathered round a large cake with the phrases “FudCo” painted in icing.

Since that story ran, KrebsOnSecurity has heard from this Saim Raza identification on two events. The primary was within the weeks following the Sept. 2021 piece, when one in every of Saim Raza’s identified e mail addresses — bluebtcus@gmail.com — pleaded to have the story taken down.
“Hey, we already depart that fud and many others earlier than 12 months,” the Saim Raza identification wrote. “Why you put up us? Why you destroy our lifes? We by no means hurt anybody. Please take away it.”
Not wishing to be manipulated by a phishing gang, KrebsOnSecurity ignored these entreaties. However on Jan. 14, 2024, KrebsOnSecurity heard from the identical bluebtcus@gmail.com deal with, apropos of nothing.
“Please take away this text,” Sam Raza wrote, linking to the 2021 profile. “Please already my police register case on me. I already depart all the pieces.”
Requested to elaborate on the police investigation, Saim Raza mentioned they have been freshly launched from jail.
“I used to be there many days,” the reply defined. “Now again after bail. Now I wish to begin my new work.”
Precisely what that “new work” would possibly entail, Saim Raza wouldn’t say. However a brand new report from researchers at DomainTools.com finds that a number of computer systems related to The Manipulaters have been massively hacked by malicious data- and password-snarfing malware for fairly a while.
DomainTools says the malware infections on Manipulaters PCs uncovered “huge swaths of account-related information together with a top level view of the group’s membership, operations, and place within the broader underground financial system.”
“Curiously, the big subset of recognized Manipulaters clients look like compromised by the identical stealer malware,” DomainTools wrote. “All noticed buyer malware infections started after the preliminary compromise of Manipulaters PCs, which raises numerous questions relating to the origin of these infections.”
A lot of questions, certainly. The core Manipulaters product lately is a spam supply service known as HeartSender, whose homepage overtly advertises phishing kits concentrating on customers of assorted Web firms, together with Microsoft 365, Yahoo, AOL, Intuit, iCloud and ID.me, to call just a few.
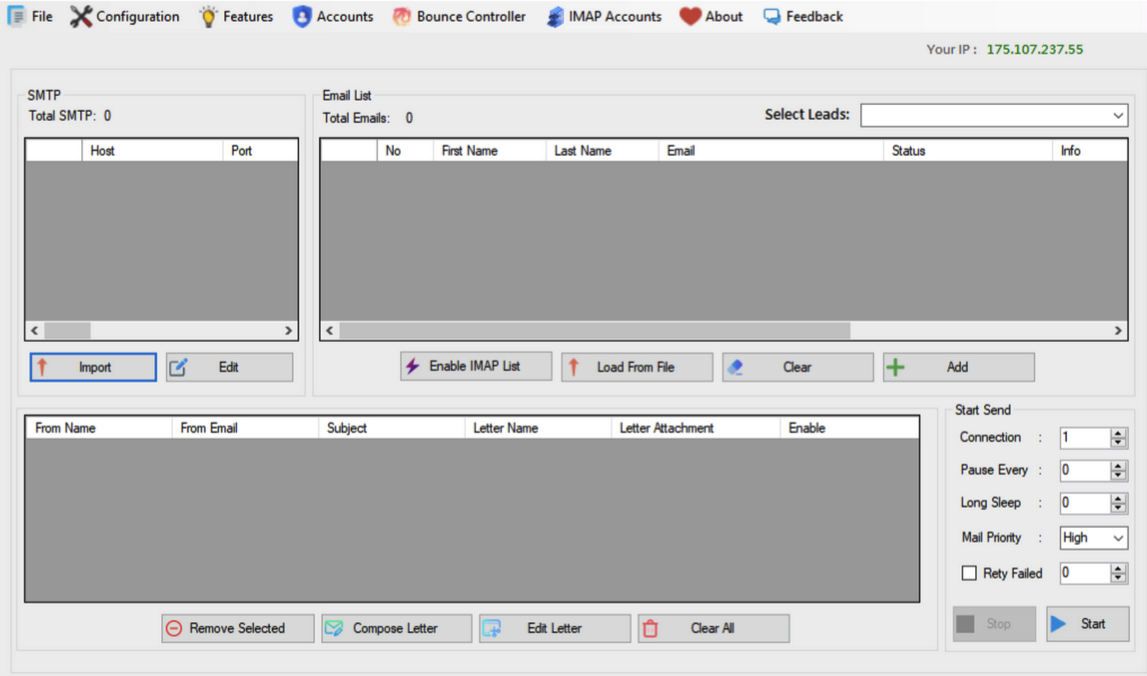
A screenshot of the homepage of HeartSender 4 shows an IP deal with tied to fudtoolshop@gmail.com. Picture: DomainTools.
HeartSender clients can work together with the subscription service through the web site, however the product seems to be far simpler and user-friendly if one downloads HeartSender as a Home windows executable program. Whether or not that HeartSender program was one way or the other compromised and used to contaminate the service’s clients is unknown.
Nevertheless, DomainTools additionally discovered the hosted model of HeartSender service leaks a rare quantity of person data that most likely shouldn’t be meant to be publicly accessible. Apparently, the HeartSender net interface has a number of webpages which are accessible to unauthenticated customers, exposing buyer credentials together with help requests to HeartSender builders.
“Satirically, the Manipulaters might create extra short-term danger to their very own clients than legislation enforcement,” DomainTools wrote. “The info desk “Person Feedbacks” (sic) exposes what look like buyer authentication tokens, person identifiers, and even a buyer help request that exposes root-level SMTP credentials–all seen by an unauthenticated person on a Manipulaters-controlled area. Given the danger for abuse, this area won’t be printed.”
That is hardly the primary time The Manipulaters have shot themselves within the foot. In 2019, The Manipulaters didn’t renew their core area identify — manipulaters[.]com — the identical one tied to so most of the firm’s previous and present enterprise operations. That area was rapidly scooped up by Scylla Intel, a cyber intelligence agency that focuses on connecting cybercriminals to their real-life identities.
Presently, The Manipulaters appear targeted on constructing out and supporting HeartSender, which makes a speciality of spam and email-to-SMS spamming providers.
“The Manipulaters’ newfound curiosity in email-to-SMS spam may very well be in response to the large improve in smishing exercise impersonating the USPS,” DomainTools wrote. “Proofs posted on HeartSender’s Telegram channel comprise quite a few references to postal service impersonation, together with proving supply of USPS-themed phishing lures and the sale of a USPS phishing package.”
Reached through e mail, the Saim Raza identification declined to answer questions in regards to the DomainTools findings.
“First [of] all we by no means work on virus or compromised pc and many others,” Raza replied. “If you wish to write like that faux go forward. Second I depart nation already. If somebody bind something with exe file and unfold on web its not my fault.”
Requested why they left Pakistan, Saim Raza mentioned the authorities there simply needed to shake them down.
“After your article our police put FIR on my [identity],” Saim Raza defined. “FIR” on this case stands for “First Data Report,” which is the preliminary criticism within the felony justice system of Pakistan.
“They solely get cash from me nothing else,” Saim Raza continued. “Now some officers ask for cash once more once more. Brother, there isn’t a good legislation in Pakistan simply they want cash.”
Saim Raza has a historical past of being slippery with the reality, so who is aware of whether or not The Manipulaters and/or its leaders have the truth is fled Pakistan (it might be extra of an prolonged trip overseas). Optimistically, these guys will quickly enterprise right into a extra Western-friendly, “good legislation” nation and obtain a heat welcome by the native authorities.
[ad_2]