[ad_1]
This is not the type of factor you anticipate to see posted on the official Twitter account of Trezor, the well-known cryptocurrency pockets producer.
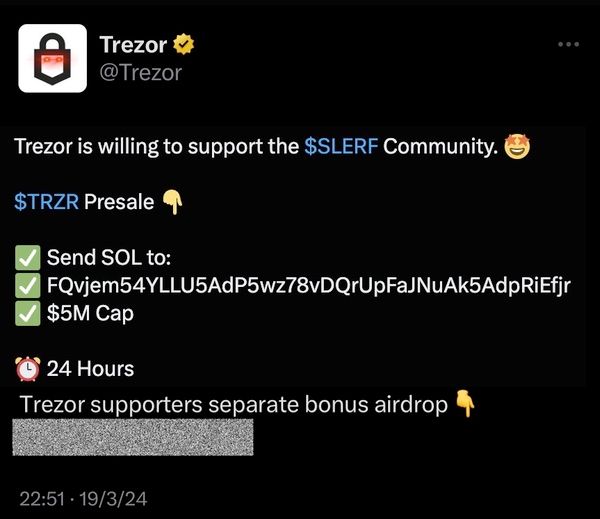
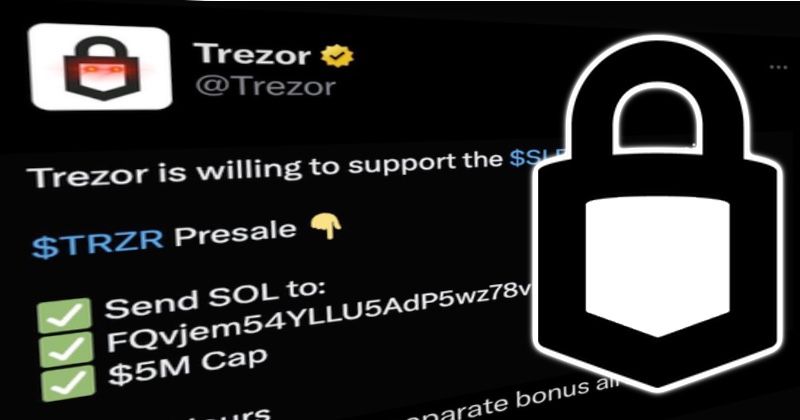
It is a pretty blatant try and dupe unwary cryptocurrency followers into transfering digital foreign money into the pockets of a scammer.
And whoever hacked Trezor’s Twitter account did not restrict themselves to only posting a rip-off. In addition they tweeted a extremely offensive message.
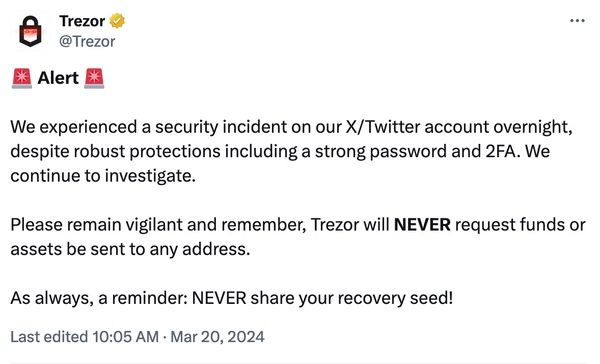
Trezor rapidly deleted the unauthorised tweets, and posted a warning to its 205,000 followers.
In a subsequent weblog put up, Trezor defined how its Twitter account had been compromised – regardless of the agency having smart safety precautions in place, similar to sturdy passwords and multi-factor authentication.
In response to Trezor, somebody posing as “a reputable entity from the crypto house”, utilizing a Twitter account with 1000’s of followers, approached its PR staff on February 29, 2024. The imposter requested to interview Trezor CEO Matej Zak.
After a number of days of “credible back-and-forth communication”, the attacker shared what gave the impression to be a Calendly invite hyperlink.
The rip-off hyperlink presupposed to be a manner of scheduling a gathering through Calendly, however finally took Trezor’s PR employee to Twitter as a substitute, which requested them to enter their login credentials.
Sensing one thing was flawed, Trezor’s staff stopped with out endangering their Twitter account.
Later, the attackers made one other profitable try to interrupt into Trezor’s Twitter account.
Feigning “technical points”, and a want to reschedule the assembly, somebody at Trezor was socially engineered into approving the authorisation request from the bogus Calendly app to attach with the official Trezor Twitter account.
Attackers may now use the faux Calendly app to put up fraudulent tweets through Trezor’s Twitter account.
Trezor emphasised to prospects that it was solely its Twitter account that was compromised by the safety incident:
We need to stress right here that the safety of all our merchandise stays unaffected. This incident has by no means impacted or compromised the safety of Trezor {hardware} wallets or any of our different merchandise. Your Trezor gadget and Trezor Suite stay protected to make use of.
Nonetheless, it is not an excellent search for the agency to have its Twitter account exploited by cryptocurrency scammers and posting racist slurs.
Be cautious when third-party apps request entry to social media accounts. I’ve had my very own private expertise of my Twitter account being exploited by hackers through a rogue third-party service.
Trezor says that it revoked all energetic periods (kicking out anybody with entry to the Twitter account) in addition to deleting the unauthorised posts, and prevented additional entry by revoking third-party apps.
This is not the primary time {that a} phishing rip-off has made the rounds, duping corporations into clicking on faux Calendly hyperlinks.
For example, in January The Verge reported {that a} scammer had posed as considered one of its journalists and pretended to be utilizing Calendly to schedule interviews with targets – all with a view to drain cryptocurrency wallets.
In the identical month, a scammer posed as one other journalist and efficiently tricked blockchain safety outfit CertiK into believing they had been scheduling a gathering through Calendly. The scammer then succeeded in seizing management of the agency’s Twitter account to put up a malicious hyperlink.
Sadly, it is not the primary time that Trezor has fallen foul of cybercriminals.
In April 2022, Trezor customers obtained a highly-convincing warning that the corporate had suffered a safety breach, and that their cryptocurrency wallets is perhaps compromised.
It later emerged that cybercriminals had hijacked management of Trezor’s MailChimp-run e-newsletter to ship out the warning. The warning tried to trick customers into downloading a malicious bogus model of Trezor Suite.
[ad_2]