[ad_1]
An software gateway, often known as an software degree gateway (ALG), capabilities as a essential firewall proxy for community safety. Its filtering functionality ensures that solely sure community software knowledge is transmitted, which has an influence on the safety of protocols together with FTP, Telnet, RTSP, and BitTorrent. Understanding ALGs entails figuring out how they work, their execs and cons, and the way they combine with or differ from different varieties of firewalls.
How Utility-Stage Gateways Work in 9 Steps
ALGs allow safe communication from the beginning of consumer requests to the mixing of complementary firewalls. They shield privateness by utilizing proxy server connections and implement safety by means of software layer and packet inspection. Additionally they successfully handle site visitors, alter packet metadata as applicable, dynamically assign assets, and apply dynamic insurance policies to enhance community efficiency and safety.
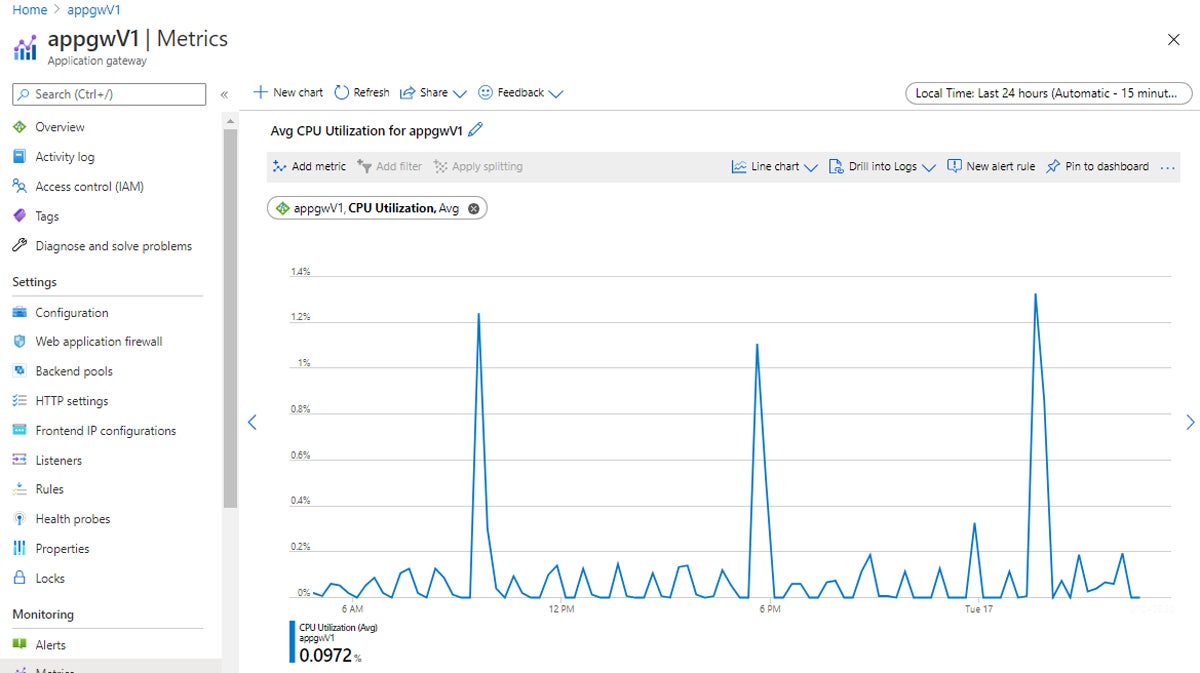
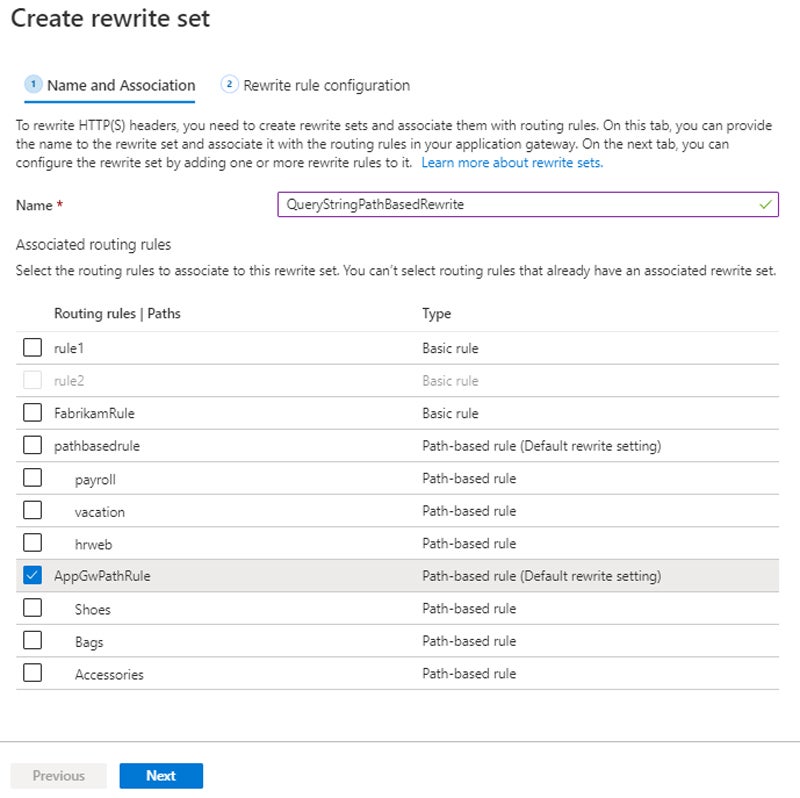
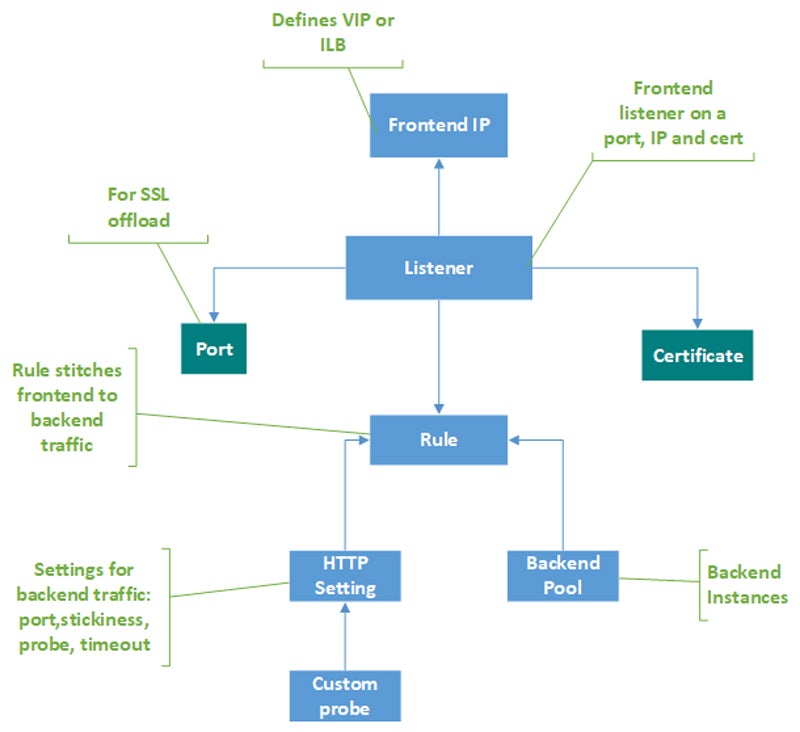
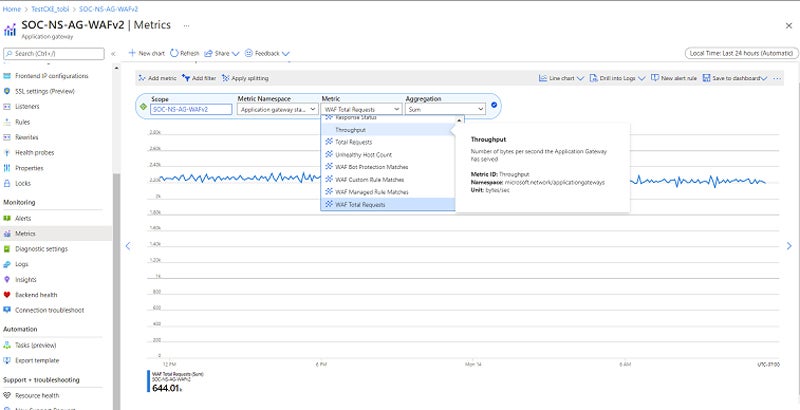
Discover the setup and optimization processes that customers can take for ALGs, in addition to the functionalities of ALGs after correct configuration. That will help you visualize the method higher, we’ve additionally supplied screenshots from Microsoft Azure’s software gateway documentation.
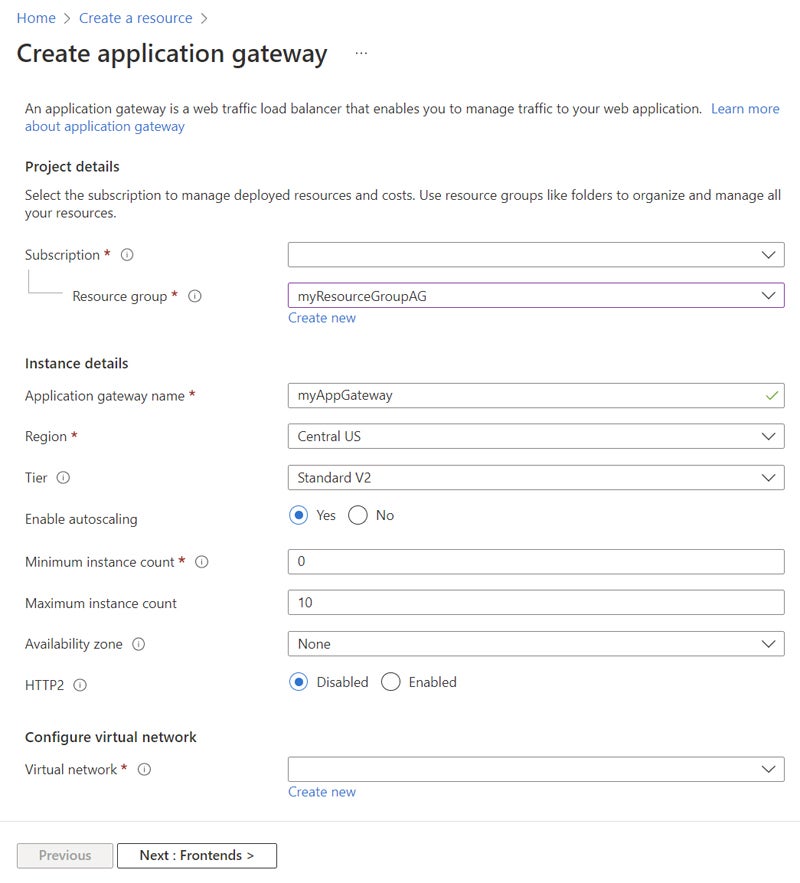
1. Customers Set Up the Utility Gateway
To create an application-level gateway, use the gateway’s interface to configure numerous choices. Begin with assigning listeners to ports, defining guidelines, and allocating assets to a backend pool. After configuration, check the gateway’s operation by accessing it by way of a browser and validating the response. Lastly, when assets are not required, clear them up by deleting the associated useful resource group.
2. ALG Facilitates the Shopper-Server Communication
When a consumer initiates a request, application-level gateways facilitate knowledge transmission between the consumer and the server. It usually entails requests for information, internet pages, or different web companies. This creates the primary connection for accessing server assets.
ALG helps consumer requests by resolving its area identify by way of DNS and delivering the frontend IP deal with to the consumer. It accepts incoming communication by means of listeners configured with frontend IP addresses and protocols. If an online software firewall (WAF) is enabled, it checks requests in opposition to WAF guidelines and both routes them to backends or blocks them. For legitimate requests, it checks routing guidelines and directs them to applicable backend swimming pools.

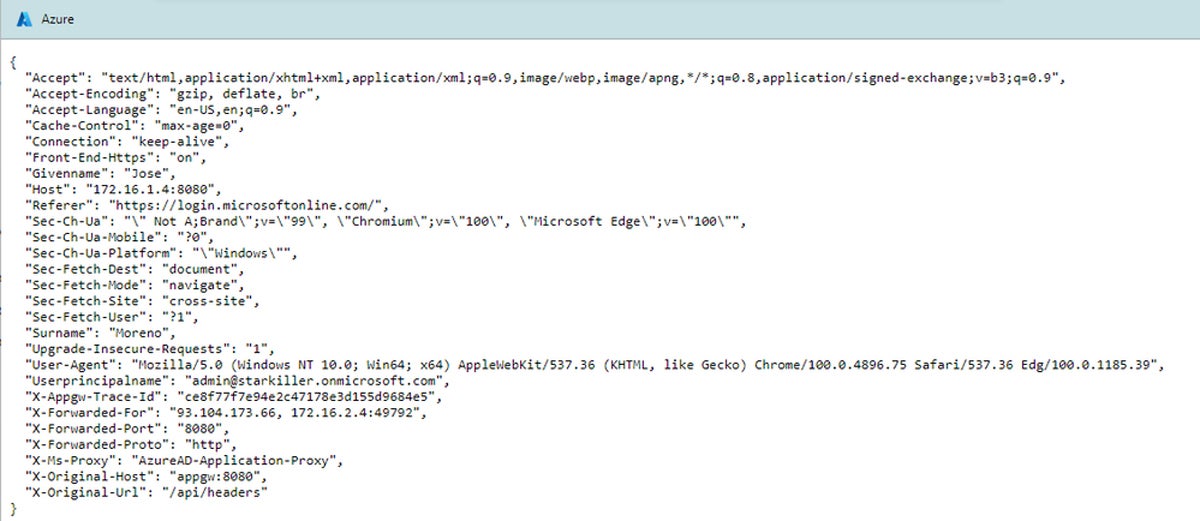
3. ALG Establishes Proxy Server Connection
Proxy server connections act as brokers, permitting purchasers to speak with most important servers. Purchasers connect with proxy servers to handle connections behind firewalls and anonymize consumer IP addresses. These servers present safe knowledge transmission, bettering privateness and safety in community interactions between purchasers and servers.
ALGs intercept and redirect consumer requests to a proxy server or gateway. The proxy server then routes the requests to the right vacation spot, resembling a backend server. ALGs can execute actions like packet inspection and modification earlier than sending site visitors to make sure safety and compliance.
4. ALG Performs Utility Layer & Packet Inspection
To make sure community safety, software layer and packet inspection work collectively in a scientific method. Initially, incoming packets are intercepted on the community interface. At OSI Layer 7, the best layer accountable for application-level communication, the firewall checks every packet’s header to find out the protocol and vacation spot port.
The payload is then completely inspected for any irregularities or safety coverage violations. If a hazard is found, an applicable measure, resembling blocking or logging, is taken in compliance with predetermined safety insurance policies. This course of is repeated for outgoing packets, and all examined packets are logged for auditing and reporting, assuring ongoing community safety.
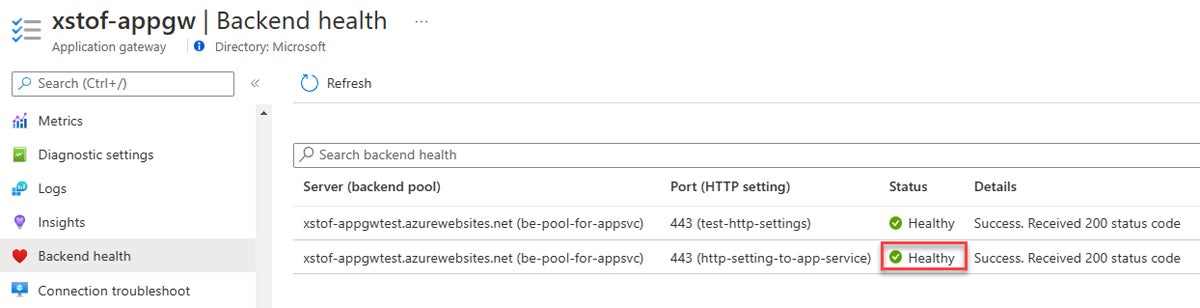
5. ALG Implements Performance & Customers Check the Backend
ALGs within the firewall acknowledge and course of site visitors for particular purposes. They determine companies utilizing Layer 4 info resembling TCP and UDP port numbers, then resolve which ALGs to make use of for every sort of site visitors. To permit ALG functionality and repair identification, the firewall have to be configured and the standards for recognizing community companies utilizing Layer 4 info have to be outlined. Every community service ought to be assigned the correct ALG.
To confirm the effectiveness of ALG, customers should do cautious testing. Tremendous-tune ALG parameters relying on check findings, and use monitoring instruments to maintain observe of ALG efficiency and backend well being. Lastly, create and implement service identification laws, and consider and replace ALG settings frequently.
6. ALG Manages Visitors
ALGs intercept each incoming and outgoing site visitors as they journey by means of the firewall. They consider packets after they’ve been intercepted to find out whose software or service they belong to. As soon as detected, ALGs monitor communication classes between purchasers and servers. ALGs handle every new session by making a session entry and mapping it to the suitable software or service.
7. ALG Modifies Packet Data
After managing site visitors, ALGs intercept and analyze packets passing by means of the firewall to seek out modifiable info resembling IP addresses or port numbers. Following preset guidelines or laws, ALGs regulate this info as wanted, probably performing community deal with translation (NAT) processing or header manipulation.
When connecting with exterior networks, NAT usually entails translating the non-public IP addresses of gadgets on the native community to a single public IP deal with allotted to the router/firewall, and vice versa. This conserves public IP addresses and will increase safety by concealing inside community construction from outdoors sources.
In some situations, ALGs might examine and alter packet payloads earlier than reassembling them to satisfy protocol necessities. High quality checks be sure that modifications meet safety and community necessities, after which ALGs transport the modified packets to their supposed locations, facilitating continued community communication.
8. ALG Allocates Sources & Applies Dynamic Insurance policies
ALGs dynamically assign assets in response to altering community site visitors calls for by consistently monitoring and altering useful resource allocation, resembling bandwidth and computing energy. All through a session, ALGs monitor site visitors for anomalies and implement dynamic insurance policies relying on site visitors traits to make sure community safety. They modify useful resource allocation primarily based on coverage enforcement and site visitors monitoring to make sure the perfect community efficiency.
ALGs launch assets after a session ends, permitting them to be reallocated for future calls for. They retailer session info, together with useful resource allocation and coverage enforcement, for auditing and reporting. This offers customers visibility into community efficiency and safety incidents.
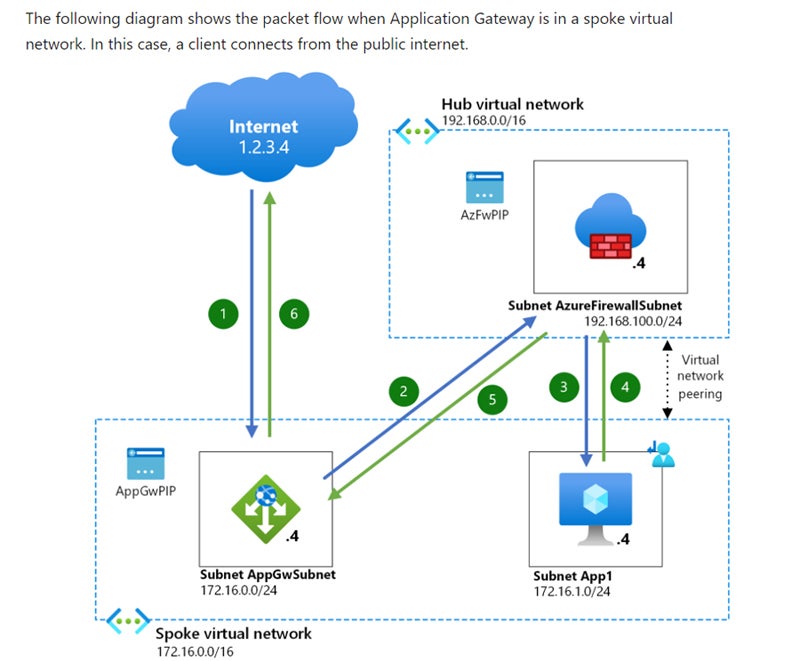
9. Customers Combine ALGs with Complementary Firewalls
To efficiently combine ALG with complementary firewalls, look at community necessities and select applicable options. Create an integration plan that outlines ALG’s place with different firewalls. Deploy and configure complementary firewalls to satisfy ALG requirements. Set ALG settings on firewalls to help the suitable purposes. Set up communication routes between ALG and firewalls. Totally check integration to make sure easy operation.
Implement monitoring instruments to trace efficiency and guarantee coverage compliance. Analyze the setups and fine-tune them accordingly. Often consider and replace settings to maintain up with community threats and adjustments. These strategies be sure that ALG works seamlessly with different varieties of firewalls, bettering community safety and application-level site visitors management.
5 Benefits of Utilizing ALGs
Utility-level gateways increase safety, handle app protocols, and provide detailed logging. Moreover, they enhance community efficiency and shield your privateness.
Enhanced Safety
ALGs increase community safety by implementing sturdy person authentication and authorization processes. By confirming person identities and implementing entry guidelines, ALGs forestall unlawful entry and safe delicate assets. This ensures that solely approved customers might entry community assets, reducing the danger of knowledge breaches and unlawful actions.
Granular Management Over Utility Protocols
Directors can specify specific guidelines and laws for every software utilizing ALGs to have granular management over software protocols. This enables for actual community site visitors administration whereas sustaining compliance with organizational coverage and regulatory necessities. ALGs optimize community efficiency and safety by controlling software entry whereas additionally permitting for extra environment friendly useful resource utilization.
Complete Logging
ALGs provide complete logging by documenting detailed info on community connections and exercise. This consists of statistics on person interactions, software utilization, and community site visitors patterns. Complete logging permits directors to conduct in-depth audits, successfully troubleshoot points, and analyze community utilization for billing or compliance functions.
Improved Efficiency
ALGs enhance community efficiency by caching continuously visited information, lowering the necessity for a number of retrievals from exterior servers. This caching reduces latency and saves bandwidth, particularly for continuously utilized assets. By optimizing knowledge transmission, ALGs enhance community responsiveness and person expertise and consequently improve total community efficiency and effectivity.
Ensured Privateness
ALGs strengthen privateness by performing as mediators and stopping direct exterior entry to inside assets. This method protects delicate info whereas lowering the danger of safety breaches or unauthorized entry. ALGs give a further diploma of safety by separating exterior and inside networks.
5 Weaknesses of ALGs
Regardless of their safety and efficiency benefits, ALGs face limitations with their protocol-specific configuration, UDP inefficiency, dependence on specialised information for implementation, person coaching points, and complicated configuration.
Protocol-Particular Setup
One draw back of ALG is its protocol-specific setup, necessitating particular person configuration for every software protocol. Directors should handle the complexities of quite a few protocols. This consequently provides to the complexity and upkeep points. This tailor-made methodology complicates implementation and will restrict scalability, impeding environment friendly community administration and optimization.
Inefficient with UDP-Primarily based Protocols
ALGs battle with UDP-based protocols, leading to inefficient site visitors administration. Their structure fails to accommodate the stateless nature of UDP, leading to poor efficiency and restricted software. This shortcoming limits their capability to deal with a variety of community purposes and will compromise community operations and responsiveness.
Information-Dependent Implementation
One other downside of ALGs is their knowledge-dependent implementation that calls for a radical understanding of every software protocol for setup. This dependency complicates implementation and desires particular expertise, impeding deployment. Directors will need to have in-depth information to accurately configure ALGs, thus limiting accessibility and will delay adoption in companies with out the required competence.
Person Coaching Challenges
Giant enterprises may have person coaching for implementing ALGs. Educating customers on ALG utilization is likely to be troublesome, maybe outweighing the advantages of deployment. This might hinder efficient use and acceptance. The underutilization or misconfiguration of those instruments reduces the supposed safety and efficiency advantages provided by ALGs.
Advanced Configuration & Compatibility Points
Configuring ALGs entails cautious consideration to community necessities and compatibility considerations. This complexity may end in configuration issues and compatibility considerations. Consequently, it might forestall seamless incorporation into present community infrastructures. Moreover, the intensive setup course of might trigger delays and operational disruptions.
How ALGs Combine into Totally different Firewall Architectures
Totally different firewall architectures like NGFWs, VPNs, built-in firewall home equipment, cloud-based firewalls, UTM, and WAF, present ALGs with a spread of how to optimize community safety and efficiency. ALGs can enhance site visitors administration and safety procedures by seamlessly interacting with present infrastructures, providing complete safety throughout a variety of community eventualities.
NGFW
ALGs combine into next-generation firewall (NGFW) designs by offering application-level intelligence and management. NGFWs mix conventional firewall capabilities with further performance like intrusion prevention, SSL inspection, and software administration. ALGs improve NGFWs by performing deep packet inspection on the software layer, providing exact management over software protocols and growing total safety posture.
VPN
Customers can combine ALGs and VPNs by establishing ALGs to examine and handle site visitors passing by way of the VPN tunnel on the software layer. By deploying ALGs alongside VPN gateways or concentrators, you may implement insurance policies and apply safety measures to VPN site visitors.
Built-in Firewall Home equipment
Built-in firewall home equipment incorporate firewall performance with extra safety applied sciences resembling intrusion prevention, VPN, antivirus, and content material filtering to offer complete community options. ALGs collaborate with these home equipment to offer application-layer intelligence and management and enhance firewalls by means of deep packet inspection. It optimizes community efficiency by effectively managing and prioritizing software site visitors.
Cloud-Primarily based Firewalls
Cloud-based firewalls shield cloud assets from cyberattacks. To correctly combine ALGs, deploy ALG performance within the cloud or use cloud-native ALG companies out of your firewall supplier. This consists of establishing ALGs to examine and management cloud site visitors, guaranteeing uniform safety guidelines throughout assets, and seamlessly integrating with firewall administration interfaces to allow centralized coverage administration and monitoring.
UTM Home equipment
ALGs work with unified menace administration (UTM) home equipment to offer subtle application-level intelligence and controls. Configure ALGs inside the UTM equipment with a view to analyze and handle application-level site visitors. This entails creating insurance policies and laws for particular person software protocols to maximise safety and community efficiency.
WAF
Net software firewalls (WAF) and ALGs each function on the software layer of the community stack. ALG, by means of deep packet inspection and management over software protocols, enhances WAF capabilities. It improves comprehension and administration of software protocols for extra correct detection and prevention of web-based assaults. ALGs can even increase WAF efficiency by successfully controlling and prioritizing software site visitors.
ALG vs Packet Filtering vs Stateful Inspection
Right here’s a comparability of application-level gateways, packet filtering, and stateful inspection primarily based on their complexities, screening strategies, and community efficiency influence. This additionally consists of their community topology visibility, transparency to customers, and packet inspection capabilities. Examine ALG with packet filtering and stateful inspection utilizing this desk and proceed studying under for added particulars.
| Options | ALG | Packet Filtering | Stateful Inspection |
|---|---|---|---|
| Complexity | Advanced | Easy | Reasonable |
| Screening | Primarily based on conduct or proxies | Primarily based on connection guidelines | Primarily based on communication state/context |
| Community Efficiency | Excessive influence | Low influence | Reasonable influence |
| Community Topology Visibility | Can cover from attacker | Can’t cover from attacker | Can cover from attacker |
| Transparency to Customers | Not clear | Clear | Clear |
| Packet Inspection Visibility | Full knowledge portion | Addresses and repair protocol sort | Full knowledge portion |
ALG vs Packet Filtering
ALGs present deep packet inspection on the software layer, giving exact management over software protocols and bettering safety measures. In distinction, packet filtering permits high-speed filtering utilizing easy guidelines, leading to environment friendly community site visitors processing. Whereas ALGs enhance safety by analyzing site visitors on the granular degree, packet filtering prioritizes sustaining knowledge movement by means of easy rule implementation.
ALG vs Stateful Inspection
ALGs look at and handle site visitors on the software layer, stopping undesirable entry and reconnaissance makes an attempt, whereas stateful inspection shortly detects and drops dangerous or unneeded site visitors. Whereas ALGs present tailor-made safety measures for particular software protocols, stateful inspection conducts full screening primarily based on communication state and context, guaranteeing dynamic rule software for nuanced safety insurance policies.
Backside Line: Deploy Utility-Stage Gateways For Enhanced Community Efficiency
Whereas ALGs apply packet inspection and provide granular management over software protocols, they’re merely one side of total community protection. ALGs alone can not deal with all safety points and have to be mixed with different community safety options to offer complete safety. To construct a powerful community protection plan, combine ALGs with different firewalls, intrusion detection programs, and different safety measures.
Uncover how intrusion detection and prevention programs (IDPS) and different varieties of firewalls complement application-level gateways for stronger community safety.
[ad_2]


