[ad_1]
Persistent threats resembling enterprise e mail compromise (BEC) necessitate an evolution of cybersecurity defenses to guard identities. Transitioning away from a reliance on authenticator apps and IP fencing towards a complete zero-trust framework, incorporating FIDO2 safety keys or passkeys, provides a path to safer and user-friendly authentication experiences. By embracing these applied sciences, organizations can fortify their defenses in opposition to refined cyber threats, making certain a better degree of safety in an more and more digital world.
We’ve all heard that identification is the brand new safety boundary. This alteration grew to become a actuality when software program as a service (SaaS) grew to become mainstream. What does “identification is the brand new safety boundary” imply? The extra we authenticate to cloud apps, the much less reliant we’re on firewalls to guard our identities.
CSOs appear to nonetheless be catching as much as securing identities on this new fashionable SaaS world. On February 12, 2024, Microsoft VP Alex Weinert introduced solely 38% of all authentications to M365 are protected by multifactor authentication (MFA).
One instance of why MFA is essential: The only most typical safety risk is enterprise e mail compromise (BEC). Hackers have found out {that a} phishing e mail that results in a wire switch is the bottom effort with the very best reward. The US Federal Bureau of Investigation (FBI) has acknowledged that BEC is a serious risk to the worldwide economic system with losses estimated at $50 billion from 2013 to 2022. There have been 80 occasions extra losses resulting from BEC than ransomware in 2022 ($2.7 billion versus $34 million).
Throughout that very same time, MFA adoption has elevated considerably. So why has MFA not slowed down BEC assaults? I’ve helped dozens of BEC victims over time and I’ve discovered a lot of the assaults have been preventable. Right here’s how hackers are bypassing MFA in the present day and why the FIDO Alliance’s Passkeys will assist.
The vulnerabilities of authenticator apps
Authenticator apps, designed to offer a second layer of safety past conventional passwords, have been lauded for his or her simplicity and added safety. Nonetheless, they don’t seem to be with out flaws. One important difficulty is MFA fatigue, a phenomenon the place customers, overwhelmed by frequent authentication requests or just following a single password spray assault, inadvertently grant entry to attackers. Moreover, attacker-in-the-middle (AiTM) methods resembling Evilginx2 exploit the communication between the consumer and the service, bypassing the newer code-matching expertise supplied by fashionable authenticator apps. These vulnerabilities spotlight the necessity for an evidence of the phrases and a dialogue on why such assaults are difficult to stop.
The inefficacy of IP fencing
On the floor, IP fencing, the apply of limiting entry to companies primarily based on the consumer’s IP deal with, provides an easy safety resolution. But, this methodology is more and more impractical and outdated in in the present day’s SaaS world and incompatible with the ideas of zero belief resembling assume breach.
Zero belief is a safety technique and method for designing and implementing the next set of safety ideas:
- Confirm explicitly: At all times authenticate and authorize primarily based on all accessible information factors.
- Use least privilege entry: Restrict consumer entry with just-in-time and just-enough entry (JIT/JEA), risk-based adaptive insurance policies, and information safety.
- Assume breach: Decrease blast radius and section entry. Confirm end-to-end encryption and use analytics to get visibility, drive risk detection, and enhance defenses.
That is the core of zero belief. As an alternative of believing the whole lot behind the company firewall is secure, the zero-trust mannequin assumes breach and verifies every request as if it originated from an uncontrolled community. No matter the place the request originates or what useful resource it accesses, the zero-trust mannequin teaches us to “by no means belief, all the time confirm.”
So, don’t configure an entry checklist to limit entry to somebody’s residence community, which operates on the belief that the house community is secure. Assume that the consumer, the gadget, and the community have all been compromised. Authenticate the consumer and the gadget. Follow microsegmentation. Implement host-based firewalls.
IP fencing might have a task in limiting privileged IT accounts as a fourth issue of authentication (after password, authenticator app, and gadget) for privileged IT accounts, nevertheless it doesn’t scale to common customers due to the appearance of privateness options in working methods like Apple’s iOS (starting in model 15) make IP fencing unrealistic since all connections are shielded behind Cloudflare. Safety operations middle (SOC) analysts battle to establish these connections if the identification system isn’t designed to authenticate each the consumer and the gadget.
Once I see IP fencing deployed, I see gaps in insurance policies to make exceptions for BYOD gadgets. It’s because authenticating a BYOD gadget isn’t simply achievable with out the consent of the worker. Ninety-five % of organizations allow their staff to make use of private gadgets. It isn’t potential to have an IP fence tied to a consumer’s identification when customers are permitted to make use of their private telephones since most customers push again and don’t allow IT to put in company cellular gadget administration (MDM) apps on their private gadgets. That is the commonest criticism I hear from IT departments in the present day.
Attackers can exploit the inevitable hole that will get created when IP fencing is just utilized to Home windows and macOS and cellular gadgets are excluded. The hacker can merely replace their internet browser to emulate a cellphone, and they’re in.
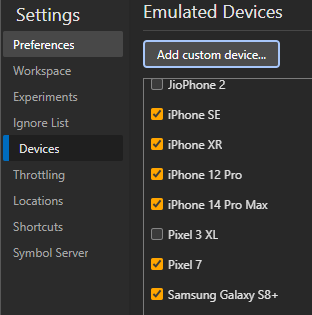
Microsoft Chromium Edge and Chrome Developer Instruments enable consumer agent emulation (spoofing)
Joe Stocker
This user-agent spoofing erodes the reliability of IP-based controls, which can’t be reliably utilized to BYOD cellular gadgets (with out the consumer consenting to enrolling their cellphone into MDM, deploying a cert, or putting in a VPN). This highlights the need of evolving past static protection mechanisms and embracing the zero-trust paradigm.
The position of FIDO2 and gadget compliance
The constraints of MFA and IP fencing underscore the urgency for adopting a zero-trust safety framework. FIDO2, with its hardware-based tokens, provides a big leap in safety by offering sturdy phishing resistance. When mixed with gadget compliance checks by way of an MDM resolution resembling Microsoft Intune or VMware Workspace ONE, organizations can be certain that solely safe, up-to-date gadgets acquire entry to delicate sources. This technique not solely addresses the shortcomings of earlier strategies but in addition aligns with the zero-trust precept that trusts nothing and verifies the whole lot.
Navigating compatibility: The combination of passkeys
Whereas bodily FIDO2 safety keys (resembling Yubikeys) characterize a big development in passwordless and phishing-resistant authentication, compatibility points, significantly on cellular gadgets, posed challenges to adoption, particularly in Microsoft Enterprise outlets. It was too technically difficult for non-technical finish customers to combine them with their private telephones. There was no full resolution since authenticator apps are usually not but phishing-resistant. Lastly, the reliance on bodily safety keys launched logistical hurdles and prices.
The modern idea of passkeys provides a promising resolution. Primarily based on FIDO requirements, passkeys are a alternative for passwords that present sooner, simpler, and safer sign-ins to web sites and apps throughout a consumer’s gadgets. Not like passwords, passkeys are all the time sturdy, phishing-resistant, and device-bound, eliminating the necessity for extra {hardware}. Passkeys simplify the consumer expertise by eliminating the password. Microsoft’s initiative to combine passkeys into their conditional entry authentication options in Microsoft Entra ID as early as March 2024 marks a pivotal step towards simplifying and strengthening authentication practices and follows by way of on the joint dedication that Apple, Google, and Microsoft made on Might 5, 2022, to undertake the passkey customary. Apple made good on their dedication with the combination of Passkeys in iOS 16, and Google did so within the fall of 2023.
The benefits of passkeys
Passkeys stand out for his or her inherent phishing resistance, as they’re tied to each the gadget and the precise service, mitigating network-based AiTM proxy assaults resembling Evilginx2. This shifts the battle to defending in opposition to major refresh token theft on the Home windows gadget.
Passkeys not solely improve safety but in addition enhance the consumer expertise by eliminating the necessity to handle bodily tokens. The shift to passkeys represents an economical technique for organizations, lowering the overhead related to distributing and changing bodily tokens.
Authentication, Identification and Entry Administration, Multi-factor Authentication
[ad_2]


